As palm vein recognition technology becomes widely adopted in payment, e-KYC, and identity verification systems, one common misunderstanding continues to appear:
Are registration and authentication the same process?
From a user perspective, both involve placing a hand over a device.
But from a biometric system and algorithm design perspective, they are fundamentally different.
At X-Telcom, understanding this difference is critical to building accurate, secure, and scalable palm vein systems.
What Is Palm Vein Registration?
Palm vein registration, also known as enrollment, is the process of creating a high-quality biometric template for a user.
This is a one-time process, but it determines the performance of the entire system going forward.
Key Characteristics of Registration:
- High image quality requirements
- Zero tolerance for capture errors
- Multi-layer validation to ensure long-term stability
- More processing time is acceptable
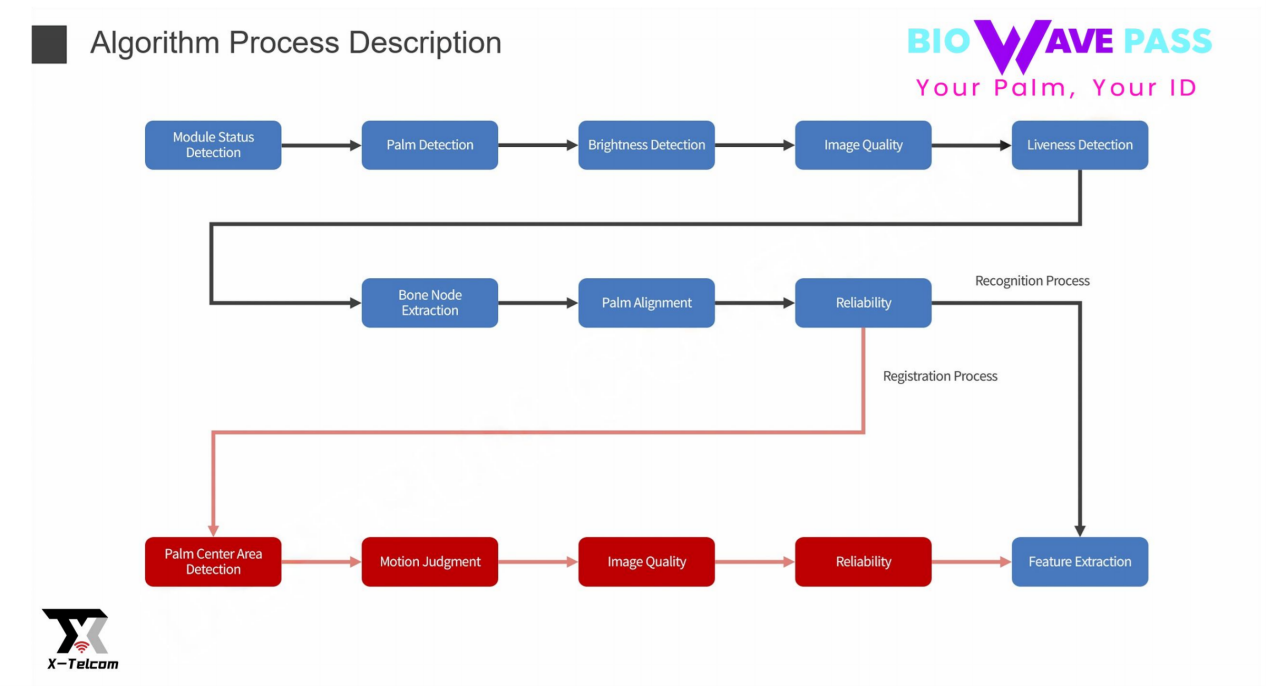
What Happens During Registration?
Unlike simple scanning, registration involves several critical steps:
- Palm center region detection to ensure standardized capture area
- Motion judgment to prevent blur caused by hand movement
- Registration reliability verification through multi-dimensional quality checks
These steps are essential to ensure that the biometric template is:
✔ Consistent
✔ Stable over time
✔ Suitable for large-scale matching
If these steps are skipped or compromised, the system will generate low-quality baseline data, which will negatively impact all future authentication accuracy.
What Is Palm Vein Authentication?
Palm vein authentication (also called identification or verification) is the process of matching a user’s palm against stored biometric data.
This happens every time a user performs an action, such as making a payment.
Key Characteristics of Authentication:
- Designed for speed and real-time response
- Matching typically completed in under 1 second
- Optimized for high-frequency usage
- Allows minor variation in capture conditions
Authentication focuses on efficiency, not deep validation.
Core Issue: Fundamental Differences in Technical Objectives:
| Dimension | Identification Flow (Blue Path) | Registration Flow (Red Path) |
|---|---|---|
| Primary Objective | Fast matching, passage efficiency | Establishing high-quality biometric baseline |
| Quality Requirements | Lenient (sufficient for matching) | Strict (must ensure long-term stability) |
| Computing Resources | Lightweight, low latency | Complex algorithms, deep verification |
| Error Tolerance | Allow a certain level of collection error rate | Zero tolerance, must succeed on first attempt |
| Timeliness | Real-time response (<1 second) | Acceptable longer processing time |
As shown in the flowchart, the registration flow (red) contains critical steps absent from the identification flow (blue), the registration flow contains critical steps that do not exist in the identification flow, including:
Why This Difference Matters
In real-world deployments, this distinction directly impacts:
- System accuracy
- User experience
- Scalability
- Security compliance
A common question is:
“Can we combine registration and authentication into one step?”
From a technical standpoint, this is not recommended.
Why Registration and Authentication Should Not Be Combined
1. Registration Requires Additional Validation
Registration includes critical steps that do not exist in authentication:
- Standardized positioning
- Motion control
- Multi-dimensional quality verification
Skipping these steps would result in uncontrolled biometric quality, leading to long-term accuracy issues.
2. Performance Trade-Off
Registration is designed for accuracy, while authentication is designed for speed.
Combining both would result in:
- Slower transactions
- Poor user experience
- Reduced system efficiency
3. System and Hardware Constraints
Running both high-quality registration logic and real-time matching simultaneously would significantly increase:
- Device computing requirements
- Processing latency
- System complexity
4. Security and Compliance
Biometric data is highly sensitive.
Temporary reuse or caching of biometric data across flows may violate:
- Data protection regulations
- Security best practices
A clear separation ensures compliance and reduces risk.
Recommended System Design by X-Telcom
At X-Telcom, we recommend a two-stage architecture:
Step 1: Registration (One-Time)
- Capture high-quality RGB and IR palm data
- Perform full validation and reliability checks
- Generate a stable biometric template
Step 2: Authentication (Ongoing)
- Perform fast palm scans
- Match against stored templates
- Complete transactions in real time
Building Scalable Palm Vein Systems
A well-designed palm vein system must balance:
✔ Accuracy
✔ Speed
✔ Security
✔ Scalability
This balance can only be achieved when registration and authentication are properly separated.
Final Thoughts
Palm vein recognition is not just about capturing a hand image.
It is about building a reliable biometric system that performs consistently over time.
At X-Telcom, our approach is based on real-world deployments across payment and identity systems.
Because in biometrics:
👉 The quality of registration defines the success of every authentication.
Learn more about X-Telcom palm vein solutions:
https://x-telcom.com/palm-vein-reader/