In biometric system deployments, one question frequently arises from fintech platforms, payment providers, and system integrators:
Can a user scan their palm once, attempt identification, and if the system cannot find a match, automatically use that captured data to register a new ID?
From a user experience perspective, the idea is attractive.
One scan, no repeated interaction, and a faster onboarding process.
Technically, this workflow can be implemented.
However, in real-world biometric deployments, feasibility does not always mean it is the right architectural choice.
Understanding why requires looking at how identification and registration fundamentally differ.
Identification Failure Does Not Mean a New User
A failed identification attempt does not necessarily mean the person is not already registered.
In palm vein systems, identification can fail for several reasons:
- Palm angle deviation
- Incorrect hand placement
- Partial coverage of the capture area
- Minor hand movement during scanning
- Illumination variation
- Conservative matching thresholds
For example, a registered user may place their palm at a slightly different angle.
The system may not confidently match the stored template.
In a properly designed system, the user would simply be asked to reposition their palm and try again.
However, if the logic were:
Identification fails → Automatically register
then the system might treat the same individual as a new user and create a second biometric identity.
At scale, this leads to duplicate registrations and database contamination.
Why Duplicate Biometric IDs Are Dangerous
Biometric systems depend on database integrity.
Once duplicate templates enter the system, several problems emerge:
- The same person may have multiple IDs
- Identification confidence declines
- False rejection rates increase
- Database maintenance becomes difficult
- Large deployments experience progressive performance degradation
In large-scale environments such as banking networks or national identity systems, even a small percentage of duplicate enrollments can significantly impact system reliability.
For this reason, registration must always be treated as a controlled identity creation process, not as a fallback branch of identification.
Identification and Registration Have Different Quality Requirements
Although both processes begin with palm capture, they serve very different purposes.
Identification is a comparison process.
It determines whether the captured sample matches an existing identity.
Registration creates a permanent biometric identity.
Because of this, enrollment requires stricter validation, including:
- Higher image quality thresholds
- Stable geometric alignment
- Consistent structural feature extraction
- Confirmed liveness detection
- High-confidence duplicate checks against the database
Using identification-grade capture data directly for enrollment risks permanently storing suboptimal templates.
Once written to the database, these templates influence future recognition accuracy.
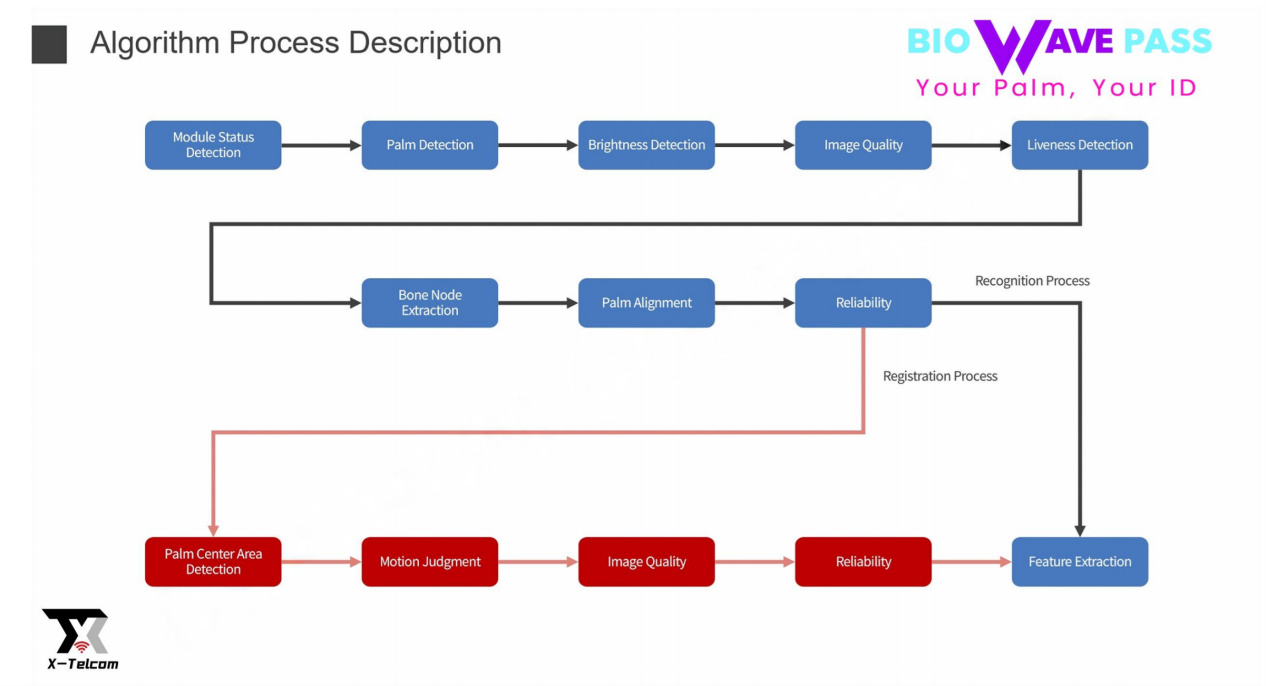
How X-Telcom Solves This Problem
In the X-Telcom Palm Vein algorithm architecture, registration is never treated as a simple extension of identification.
Although a single capture can technically be reused, the system does not allow automatic enrollment based solely on a failed identification attempt.
Instead, the architecture introduces multiple control layers before a new biometric ID can be created.
These include:
- Multi-layer capture validation
- Structural landmark extraction and palm alignment
- Strict reliability scoring mechanisms
- Enrollment-grade image quality thresholds
- Advanced liveness verification
- Pre-enrollment duplicate detection
These controls ensure that identification remains fast and seamless while registration is protected against duplicate or low-quality enrollments.
Why This Architecture Matters
Palm vein authentication is increasingly used in environments such as:
- Banking and fintech payment systems
- Retail payment terminals
- Government identity programs
- Large-scale access control networks
In these deployments, the long-term health of the biometric database is critical.
Once duplicate identities or poor-quality templates enter the system, performance degradation becomes extremely difficult to reverse.
That is why X-Telcom separates identification logic from enrollment authorization, even when the user interaction appears simple.
From the user’s perspective, the experience remains seamless.
Behind the scenes, strict biometric governance protects system integrity.
The Key Principle
A single scan can provide a smooth user experience.
But biometric registration must never be triggered automatically by identification failure.
Responsible biometric architecture requires:
- Strong enrollment validation
- Identity uniqueness enforcement
- Database hygiene
- Fraud resistance
- Long-term recognition stability
This is the foundation of the X-Telcom Palm Vein algorithm design philosophy.
User experience should be simple.
System integrity must always remain uncompromised.
Learn more from: https://x-telcom.com/palm-vein-reader/